I love Let’s Encrypt. It’s free SSL, it’s safer because of the auto-renewal and it’s so easy to setup. No more emailing around validating company name and all that hassle.
Before you start you do need to have opened your router to the outside world.
The installation on server level has also got a lot easier in the past years. The following will work for both Raspbian and Ubuntu.
For other systems check the official site, just select the correct OS and webserver.
Install Certbot
Let’s Encrypt will work through a program called Certbot. We will install Certbot and that will get the free SSL certificates from Let’s Encrypt.
To install run these 2 commands, these might take a while:
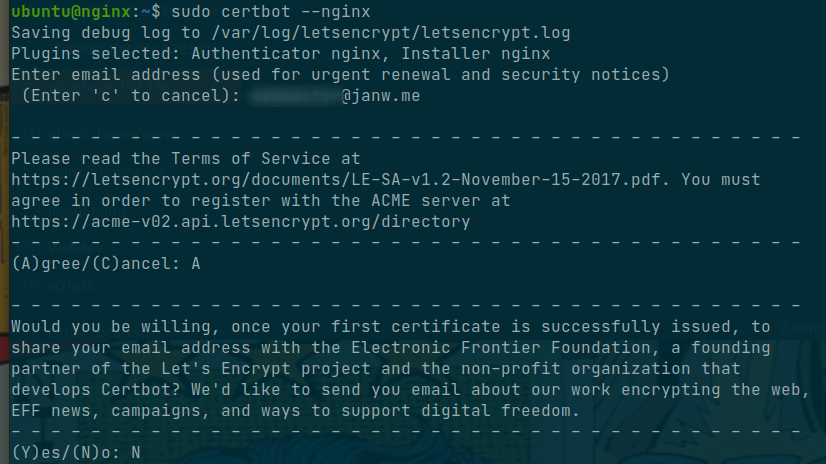
sudo apt install certbot python3-certbot-nginxOnce this is done we can start getting the SSL-certificates. Run:
sudo certbotSince it’s the first time running it will ask for email and some other stuff.
For the next step you can select specific domains, or all.
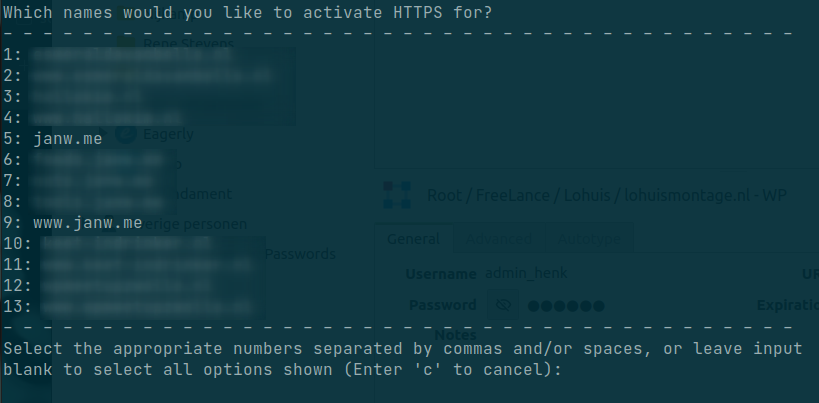
It should create and set all certificates correctly. If in the future you add a new domain just rerun the command sudo certbot --nginx and select the new domains.
Auto renewal
Let’s Encrypt certificates are valid for 90 days, this is for security reasons. This does mean they need to get renewed periodically.
By default Certbot should have installed auto renewal. But we are going to check it with the command: systemctl list-timers --all
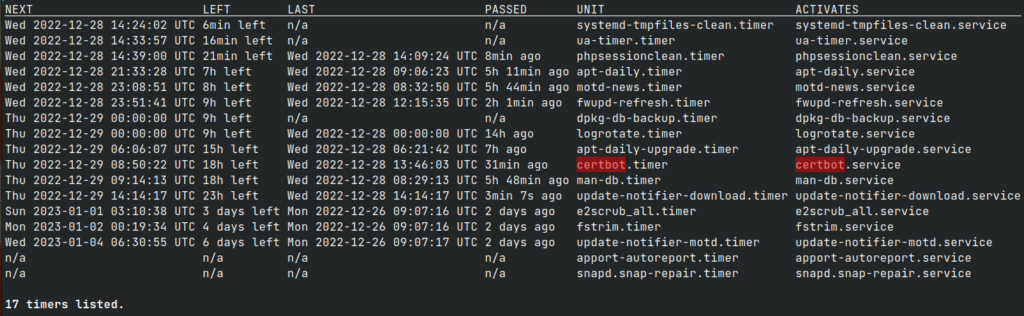
There should be some output about certbot.service.
If not we are going to setup the renewal ourself.
The command to renew the certificates is sudo certbot renew
You can also run this command by itself to test it out.
As it is run by root we will also add it to the crontab of the root user.
sudo crontab -e
Inside we add the following command.
0 0 * * 1 certbot renewHere we set it to run every Monday at 0:00 (so Sunday to Monday night)
That’s more then enough, you can run it more if you want, I would not run it less.
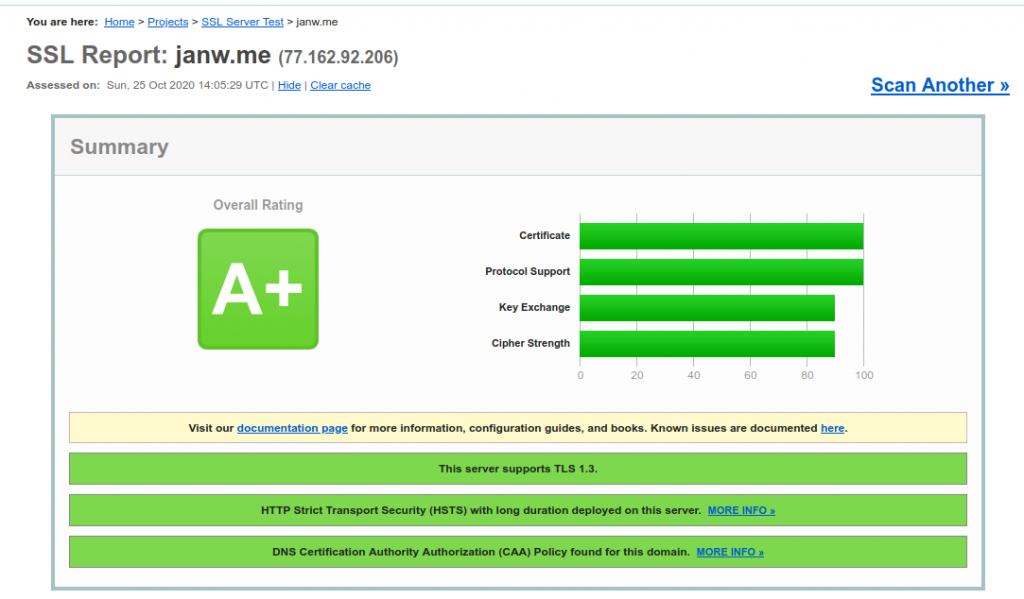
Test your SSL connection.
Finally go to ssllabs.com and test your site. Behind the scenes Certbot also adds a bunch of security settings which will help get that A+.